What is a Firewall Device and Why Does an Enterprise Need It?
In our contemporary digital landscape, characterized by pervasive connectivity, protecting our digital assets is of utmost importance. The firewall stands as a primary defense mechanism, constituting a sophisticated network security system meticulously crafted to guard our devices against cyber threats. This comprehensive guide delves into the nuances of firewalls, elucidating their diverse types, functions, and pivotal role in upholding resilient network security.
What Is a Firewall?
A firewall serves as a vigilant guardian, establishing a barrier between a user's computer and the vast network. Picture it as a digital bouncer, carefully inspecting every piece of data, seeking entry or exit from your device. Functioning as the initial line of defense, it thwarts unauthorized access and reinforces barriers against cyber intruders.
Different Types of Firewalls
Packet Filtering Firewalls:
These firewalls inspect data packets based on predefined rules, allowing or blocking traffic accordingly. Their efficiency lies in their simplicity, making them a common choice for personal use.
Stateful Inspection Firewalls:
Going beyond packet inspection, these firewalls keep track of the state of active connections. This enables them to make more nuanced decisions, enhancing security by understanding the context of data transmissions.
Proxy Service Firewalls:
This firewall operates at the application layer; proxy firewalls act as intermediaries between users and the internet. They provide an additional layer of anonymity and security by handling data requests on behalf of users.
Next-Generation Firewalls (NGFW):
NGFWs is the latest evolution; this firewall technology integrates several advanced features such as intrusion prevention, deep packet inspection, and application awareness. Providing a comprehensive approach to network security, they skillfully address the intricacies of contemporary cyber threats.
Unified Threat Management (UTM) Firewall:
A Unified Threat Management (UTM) device typically combines the functionalities of a stateful inspection firewall, intrusion prevention, and antivirus loosely interconnectedly. It may encompass supplementary services, often incorporating cloud management. The design philosophy behind UTMs emphasizes simplicity and user-friendliness.
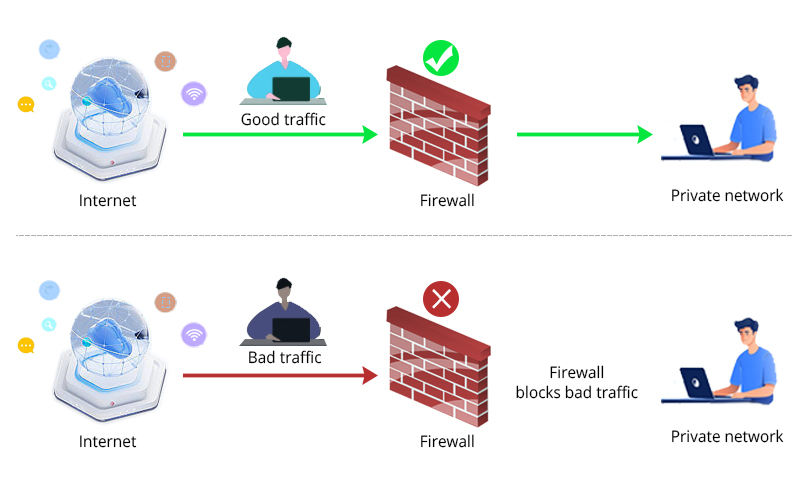
How Does a Firewall Work?
Grasping the intricacies of a firewall is vital—it parallels a meticulous customs inspection at the border, scrutinizing each information packet. The firewall evaluates data packets according to predefined rules, identifying anomalies or potential threats. A successful inspection allows the packet to proceed while flagged content is promptly blocked, ensuring only secure and authorized data traverses the network.
Why Are Firewalls Important?
In an era marked by the escalating sophistication of cyber threats, firewalls have become indispensable. Functioning as a robust shield, they are crucial in thwarting unauthorized access, safeguarding sensitive information, and standing as vigilant sentinels against a spectrum of digital adversaries, including malware and hackers.
Key Uses of Firewalls
Malware Prevention:
Firewalls play a crucial role in blocking malware from infiltrating your system. They scrutinize incoming data for known malicious patterns and prevent them from compromising your device.
Access Control:
By enforcing access control policies, firewalls limit who can access your network. This is especially critical in organizational settings where sensitive information must be guarded against unauthorized personnel.
Privacy Assurance:
Firewalls contribute to privacy by controlling data flow in and out of your network. This is essential for individuals and businesses alike to protect sensitive data from prying eyes.
Functions of Firewall
Packet Filtering:
The fundamental function of packet filtering involves examining individual data packets and deciding whether to allow or block them based on predefined rules.
Network Address Translation (NAT):
NAT plays a vital role in enhancing security by masking internal IP addresses, making it more challenging for potential attackers to identify and target specific devices.
Virtual Private Network (VPN) Support:
Firewalls frequently incorporate VPN support, enabling secure communication over the internet through the establishment of encrypted tunnels. This feature is essential for preserving the confidentiality and integrity of data transmissions.
Advantages of Using Firewall Devices
Enhanced Security:
The primary advantage of firewalls is their heightened security, safeguarding against many cyber threats.
Privacy Protection:
Firewalls contribute to privacy by controlling data flow ensuring that sensitive information remains confidential.
Peace of Mind:
Knowing that a robust firewall is in place offers peace of mind, allowing users to navigate the digital landscape confidently.
How to Use Firewall Protection?
Implementing firewall protection effectively involves installing the software. Regular updates, configuration adjustments based on specific needs, and proactive monitoring of firewall logs are essential for maintaining optimal security.
Application Layer and Proxy Firewalls
Application Layer Firewalls:
These advanced firewalls operate agt the application layer of the OSI model, providing a more granular data inspection. This allows for more effective detection of malicious activities.
Proxy Firewalls:
Proxy firewalls function as intermediaries, intercepting and scrutinizing data requests on behalf of users, providing an additional layer of security and anonymity, especially within corporate settings.
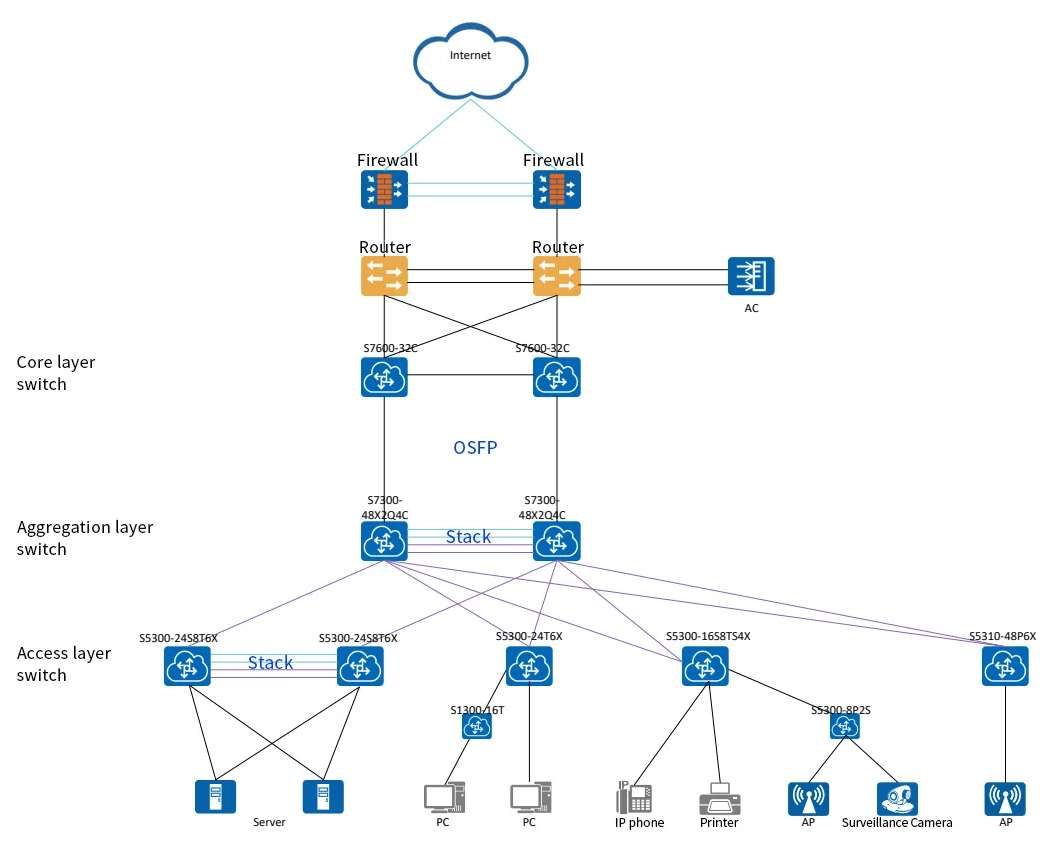
Here is a customer success story of Firewall application design by QSFPTEK in an enterprise network:
Related Product:
The Importance of NAT and VPN
Network Address Translation (NAT):
NAT is crucial for obscuring internal IP addresses, reducing the surface area for potential attacks, and making it more challenging for malicious actors to pinpoint specific devices.
Virtual Private Networks (VPNs):
VPN support in firewalls ensures secure communication by creating encrypted tunnels. This is particularly important for remote workers or organizations with geographically dispersed offices.
The Future of Network Security
Looking ahead, the future of network security involves integrating artificial intelligence and machine learning into firewall systems. These technologies enable adaptive and proactive defenses, identifying and mitigating emerging threats in real-time.
It's essential to clarify the distinction between firewalls and antivirus software. While firewalls focus on controlling and monitoring network traffic, antivirus software is designed to detect and remove malicious software from individual devices.
While firewalls are a crucial network security component, they have limitations. They may not be effective against certain attacks, and internal threats can still pose risks. Emphasize the need for a layered security approach, combining firewalls with other security measures.
Conclusion
In conclusion, firewalls are the unsung heroes of the digital realm, tirelessly protecting our devices and networks from a myriad of cyber threats. By understanding their types, functions, and network security landscape, individuals and organizations can fortify their digital fortresses and confidently navigate the online world. Stay informed, stay secure.











